If you want to protect your privacy online, you need to know about and start using Tor. In this article, we will talk about what Tor is, along with who uses it and why. From there, we’ll get into exactly how Tor works, how it provides anonymity, and the limitations of the service. We’ll finish up by walking through downloading, installing, and starting to use Tor on your own computer.
What Is Tor?
Tor began its life in the 1990s when researchers at the US Naval Research Laboratory developed “onion routing.” Onion routing makes it possible to pass messages through a network anonymously. It uses multiple layers of encryption that get peeled off one by one (like peeling an onion) as the message passes through multiple nodes in the network.
In 2004, the Navy released the second generation of Tor. In 2006, researchers involved in Tor incorporated the Tor Project and took responsibility for maintaining Tor.
Tor stands for the onion router. It is a network of thousands of computers around the world that implements onion routing. Originally designed to protect US Intelligence Agency communications online, it now serves millions of users, military, government, and civilian, in every country on Earth.
Here is the Table of Contents of the remainder of this tremendous resource.
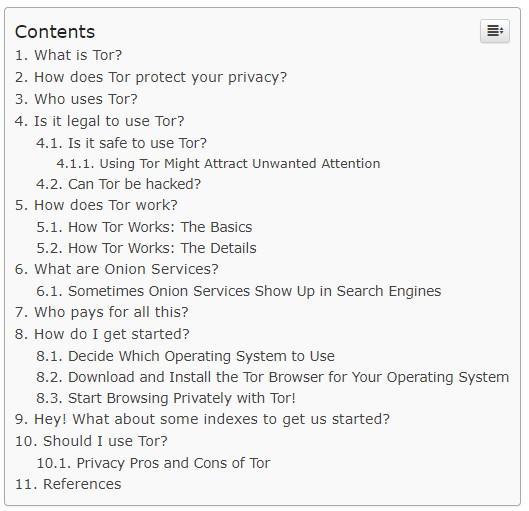
Continue reading the rest of the article from our friends at blokt.com - CLICK HERE!